User Tools
Sidebar
Table of Contents
Commands to Multiple Devices
Toolbox
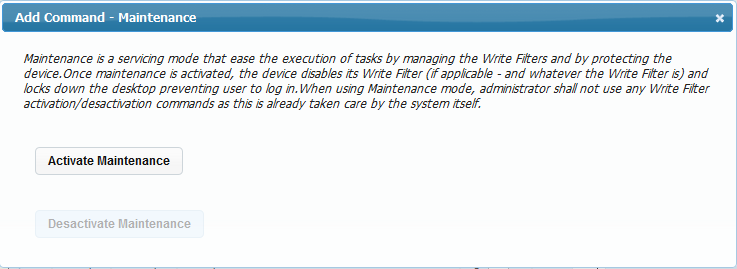
Maintenance
Occasionally, tasks must be performed on a device with the protective Write Filters disabled. It is not advisable to allow users to use the device while the task is running, as it may interfere with the management process. In such circumstances, use the Maintenance command.
When Maintenance is activated, Xcalibur W Agent places the device into maintenance mode. This locks out all keyboard and mouse activity from the user. Maintenance mode also disengages the Write Filter (FBWF or EWF) so any maintenance tasks performed are persistent.
When Maintenance mode is deactivated, the FBWF or EWF is switched on and the device is rebooted.
Sleep
The Sleep command inserts a pause into a command sequence. The Agent executes the next command after pausing for the duration entered. The duration must be set in seconds.
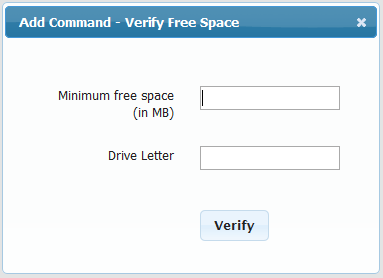
Verify Disk Space
The Verify Disk Space command checks the free space available on the target device. If there is enough disk space, then the command returns a success. If there is not enough disk space, the command returns an error.
This command is useful when an application must be installed or new files loaded. By using the ”“Verify Disk Space”” linked  to the next command, the installation will only be performed if the system has the necessary space available.
to the next command, the installation will only be performed if the system has the necessary space available.
Flush Agent Command Queue
Use the Flush Agent Command Queue command to stop and purge all commands that have already been received by the agent.
Monitor
The Monitor command consists of two further Level 2 commands: Inventory and Diagnostics.
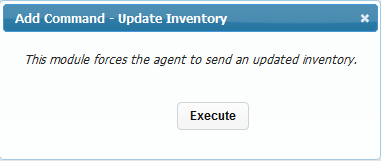
Inventory
Run the Inventory command to instruct the devices in the selection to update their inventory to the Xcalibur W. This inventory update can also be done at startup of every device if required.
To view the inventory of a particular device, simply double-click on its device listing entry.
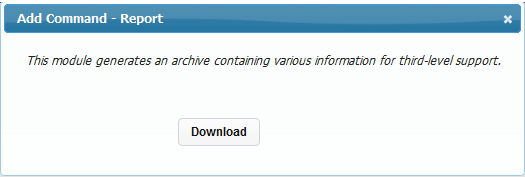
Diagnostics Report
The Diagnostic command instructs the client(s) to upload the diagnostic log to the server. The diagnostic log is in an XML format and can be sent to the support department for assistance. The diagnostic files are then downloaded to the library as compressed archives.
Interact
The Interact command section contains commands that allow you to interact with users via the device.
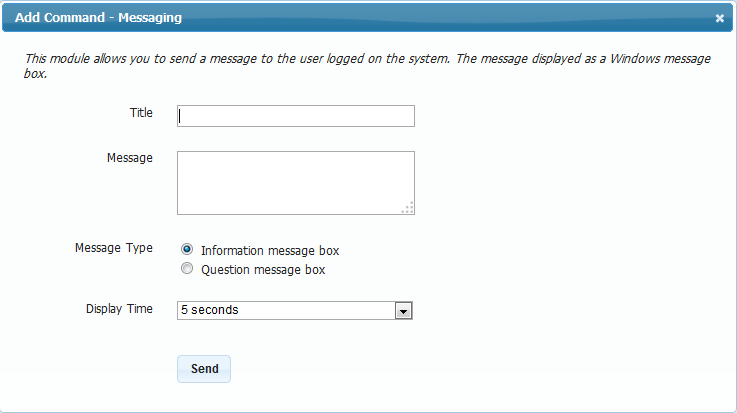
Messaging
The Messaging command sends a message to one or many devices. The messages can be simple notifications or interactive dialogs. Messages, like any other command, can be scheduled for later delivery.
 This command is executed using the Xcalibur W tray in order to be applied to the current user session. Please refer to Xcalibur W Tray section for more information This command is executed using the Xcalibur W tray in order to be applied to the current user session. Please refer to Xcalibur W Tray section for more information |
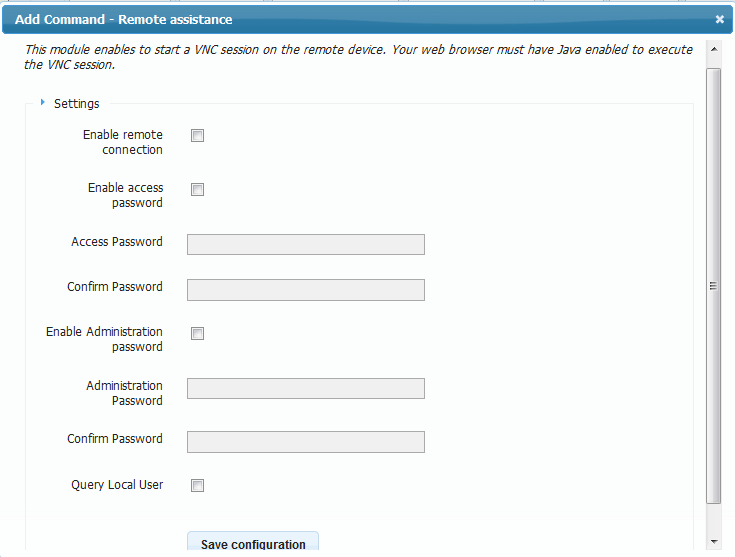
Remote Assistance
The Remote Assistance command opens a VNC session to the devices. Provide the password, and an administrator password for full rights on the device.
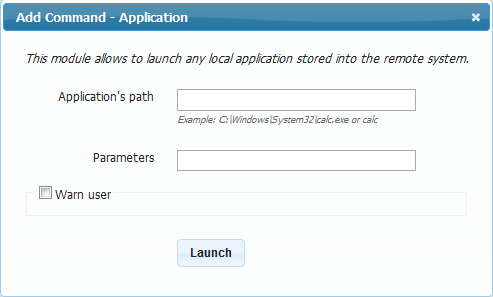
Launch Application
To run applications on the target device, use the Launch Application command.
To use the Launch Application command, enter the full path to the application, and any runtime parameters that are needed. You can also warn the user by sending a message. Click Launch to proceed.
 This command is executed using the Xcalibur W tray in order to be applied to the current user session. Please refer to Xcalibur W Tray section for more information This command is executed using the Xcalibur W tray in order to be applied to the current user session. Please refer to Xcalibur W Tray section for more information |
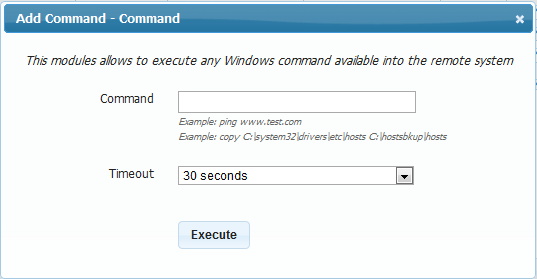
Launch Command
Use the Command command to run shell commands on the target device(s). Specify the command name or path and any necessary parameters, and then click Execute.
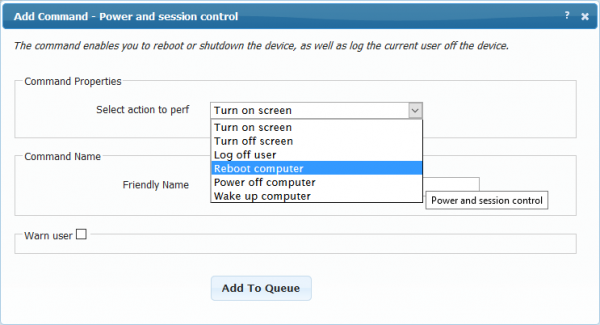
Power & Session Control
The Power and Session Control command allows administrators to perform a number of low-level user session commands, including
- Turn Screen On
- Turn Screen Off
- Log Off
- Reboot
- Shutdown
- Wake Up Computer using Wake On Lan
Agent Administration
The Agent Administration command set contains commands required to configure the device’s agent.
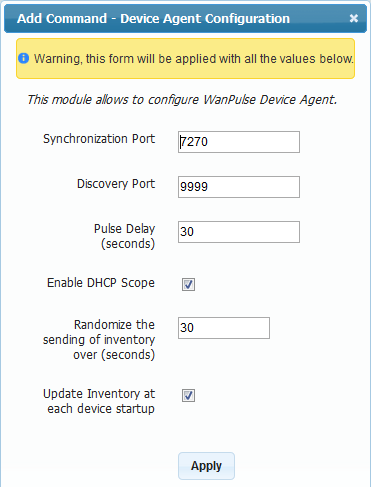
Agent Configuration
Although the Xcalibur W Agent installed on the device is configured for optimum performance, administrators may need to reconfigure the agent to operate within the restrictions or rules of the network.
Synchronization Port
When clients connect to the Xcalibur W Server over a LAN or a routed WAN using MPLS, for example, the pulse synchronization system uses port 7270 by default to inform the client agent that there is a Command Queue waiting for it.
When operating across a WAN that is not routed, the server awaits the pulse sent from the client and then sends the task to it.
Discovery Port
This is the port used by Xcalibur W to send and receive discovery signals.
Pulse Delay
The pulse or heartbeat is sent by the client agent on a regular basis to inform Xcalibur W Server that it is present and online. It is also used by the server to determine whether there are jobs waiting for the client in a WAN managed scenario. The entry represents the number of seconds between pulses.
Enable DHCP Scope
As mentioned in the Discovery section of this guide, Xcalibur W Agent uses DHCP to obtain the IP address or host name of the server. This behavior can be enabled or disabled by toggling the check box. The default state is enabled.
Randomize the Sending Inventory (Seconds)
Every client agent will send the device inventory at power-on. If there are hundreds or thousands of devices powering on at approximately the same time, there will be a sizable network load generated when the information is sent. This setting enables the device to randomize the sending time of the inventory to reduce network loads.
Update inventory at each device startup
If necessary, the Update inventory at each device startup setting can be disabled using the Xcalibur W Agent settings described later.
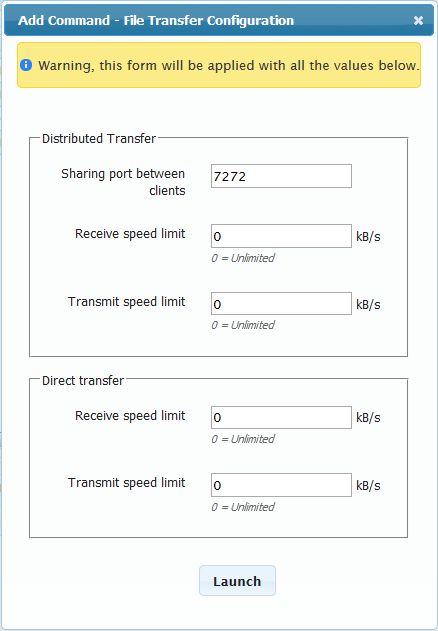
File Transfer Configuration
Direct or Distributed File Transfer
Xcalibur W Server can perform software and data updates either through distributed file transfer or through direct file transfer. Using distributed transfer mode, agents on the same LAN share the downloaded data, resulting in significant bandwidth savings. Distributed file transfer uses peer-to-peer technology. Note that both mechanisms use HTTPs connections.
For further information on Distributed file transfer, please refer to the File Transfer section within Manager Options menu.
File Transfer Settings
For each type of file transfer, the administrator can define the maximum network bandwidth the agent should allocate for transfers. This is used to guarantee that applications running on the device do not suffer from the network transfer happening in the background.
Additionally, the TCP port used for Distributed file transfer can be modified from its default value of 7272.
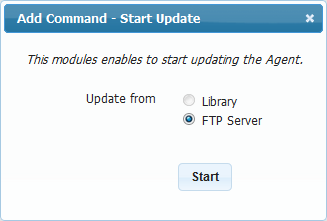
Agent Update
Xcalibur W Agent can be updated either via the Library or the FTP server.
For more information on Agent Update, refer to the Agent Update page in Advanced Section.
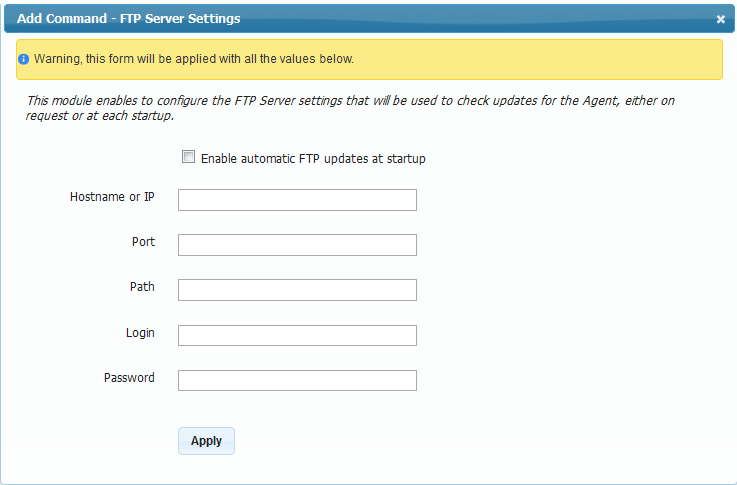
FTP Server Settings
Use the FTP Server Settings command to configure details for the management agent update system. The agent is capable of auto updating itself in the event of a version change.
To configure the settings, download the infoversion.xml file. The format of this file is as follows:
<Info>
<Imaging>
<Version>0.0.0</Version>
<Path>image15032011</Path>
</Imaging>
<Profil>
<Version>0.0</Version>
<Path>Profil0.2.txt</Path>
</Profil>
<Agent>
<Version>1.3.11.594</Version>
<Path>ftp://anonymous:test@ftpserver/xcaliburwDeviceAgent_2.12.10.2278.exe</Path>
</Agent>
</Info>
This information can also be set up for provisioning via a DHCP Scope, ID230. The format used for the scope entry is
- @WP:n.n.n.n;21;Anonymous;Test;/;true:@WP
where
- @WP: is the start of the information tag
- n.n.n.n is the IP address of the FTP Server
- 21 is the port to be used
- Anonymous is the username used to log in
- Test is the password used to authenticate
- / is the path where the infoversion.xml is kept
- True is to inform the agent that the auto-update is active.
- :@WP is the end of tag marker
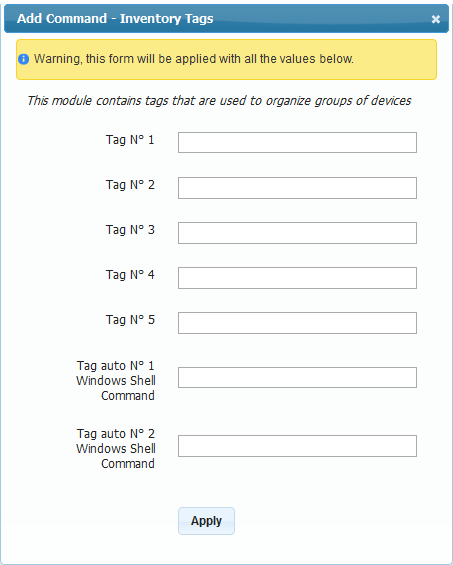
Inventory Tags
Xcalibur W Server can assign inventory tags to devices. There are two types of tags - regular (five each) and dynamic (two each).
Regular tags consist of plain, alphanumeric text. Dynamic tags can use WMIC expressions. For example, to get the time zone of a device, use a Dynamic tag such as “WMIC TIMEZONE GET STANDARDNAME”. This will return something similar to GMT Standard Time.
Inventory tags can also be used to auto-create groups. The additional power of WMIC commands allows the auto-creation of groups using a much wider set of parameters, such as time zone etc.
To assign friendly names to the tags, refer to the Personalize Section.
Device Security
The Device Security group contains commands linked to the security and operable state of the device.
Windows Accounts
Use the Windows Accounts command to change the password of a given account on the target device(s). Enter the account name in the Account field, and then tick the check box to edit the password.
The format of the password can be standard alphanumeric and symbol as Windows permits or it can be prefixed or have a suffix based on the MAC ID of the device for additional security.
Auto-Logon
By default, Windows Embedded devices are configured to log in to the USER account with default password “user”. However, in domain environments, devices normally do not auto-logon. It is preferable to use a domain login so single sign-on works seamlessly.
The Auto-logon command allows auto-login credentials, including domain name, to be configured.
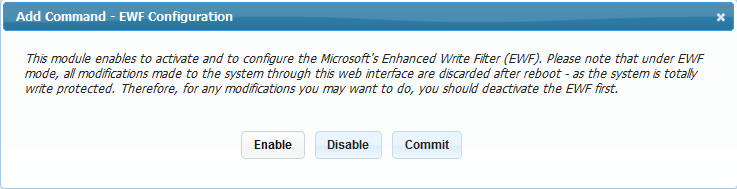
Write Filter EWF
This command controls the behavior of the Enhanced Write Filter (EWF) within Windows Embedded devices. All Xcalibur W-enabled devices are configured to have file-based write filter (FBWF),
Activating any of the options within this command will initiate a reboot sequence within the Command Queue.
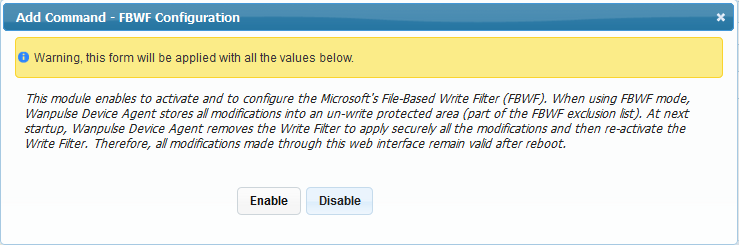
Write Filter FBWF
This command controls the File Based Write Filter (FBWF) within Windows Embedded devices.
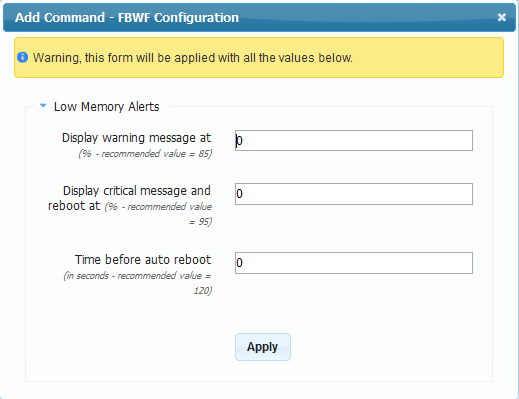
When FBWF is used on devices, Low Memory alerts may be displayed on the desktop device as a result of the low memory threshold setting, pre-programmed by Microsoft into all Windows embedded devices. The settings allow you to alter this threshold should you find any problems with this issue on your devices.
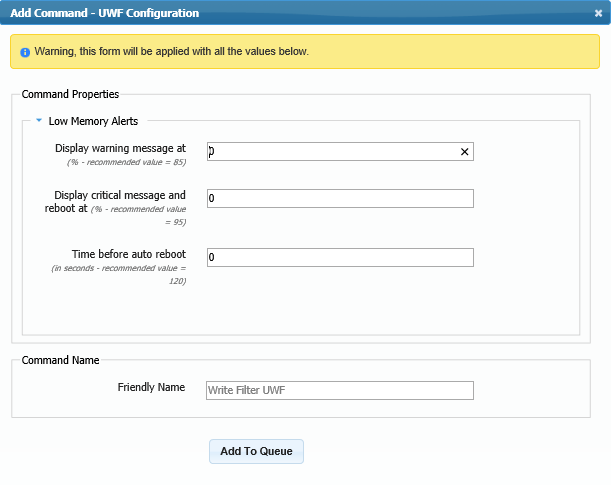
Display Warning Message at %
This field allows you to set the percentage at which the FBWF Cache will trigger a low memory warning. (Default value = 85, Minimum value = 50, Maximum value = 90)
Display Critical Message and Reboot at %
This field allows you to set the value at which the FBWF Cache has reached a critical stage and reboot of the device is required in order to flush the system. This message will be displayed in conjunction with a countdown to reboot. (Default value = 95, Minimum value = 55, Maximum value = 95)
Time before Auto-reboot (seconds)
This field allows you to set the number of seconds that will elapse before the system reboots following the Critical message described previously. This command causes a reboot command to be placed in the Command Queue.
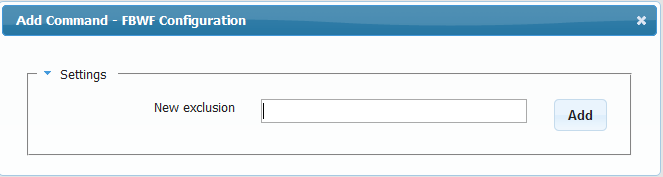
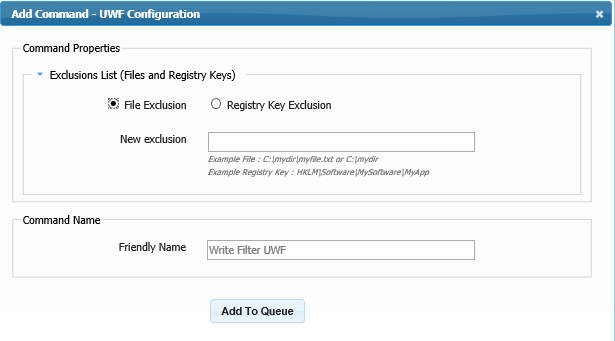
FBWF Exclusion List
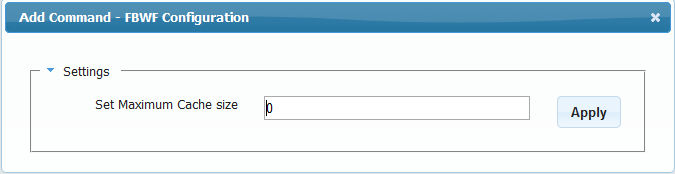
FBWF Cache Size
This option allows to define the size of the memory cache that is dedicated to the Write filter Ram overlay.
FBWF Memory Alerts
This command allows Low Memory Alerts, including warnings, critical messages, and auto-reboots, to be configured.
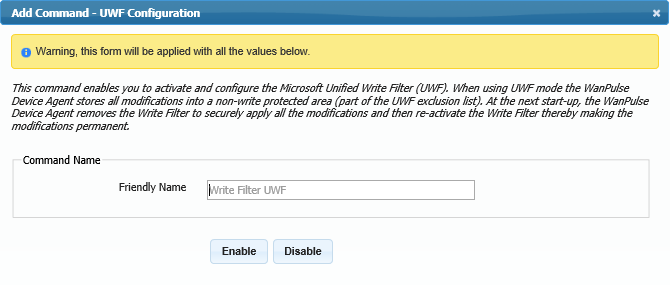
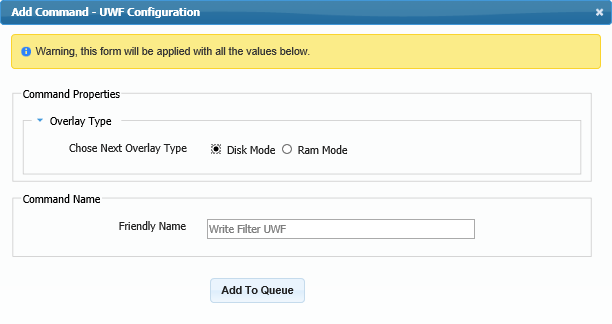
Write Filter UWF
UWF Exclusions List
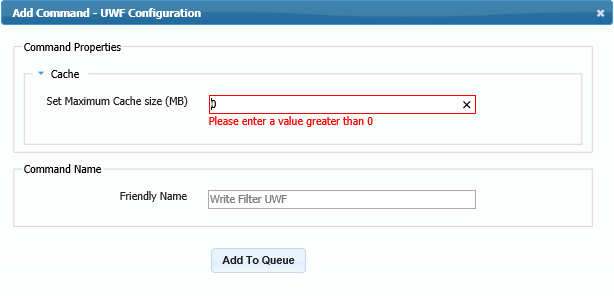
UWF Cache Size
This option allows to define the size of the memory cache that is dedicated to the Write filter space overlay.
UWF Overlay Type
This define where the space of the memory cache that is dedicated to the Write filter overlay.
You can choose to write on the disk or on the ram.
UWF Memory Alerts
This command allows Low Memory Alerts, including warnings, critical messages, and auto-reboots, to be configured.
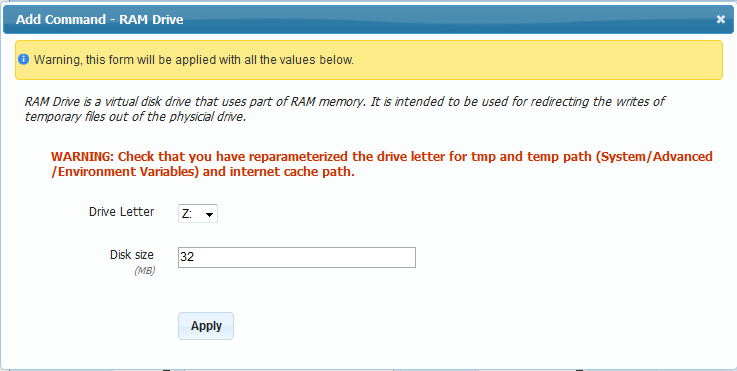
RAM drive
Use the RAM drive command to temporarily increase the size of the RAM drive on a target device (i.e. to install application updates etc.).
If the drive letter used by the RAM drive is changed, ensure other parameters that reference the RAM drive are changed to match.
The default size of the RAM drive is 64MB. The recommended maximum size of the RAM drive is 512MB.
USB Ports
One of the key concerns for IT managers is the security of the USB ports on target devices. The USB Ports command allows administrators to lock the USB ports from accessing any ‘storage class’ devices, or make them read-only.
Deploy Certificate
This command allows administrators to distribute and save a security certificate into the appropriate store.
Applications Configuration
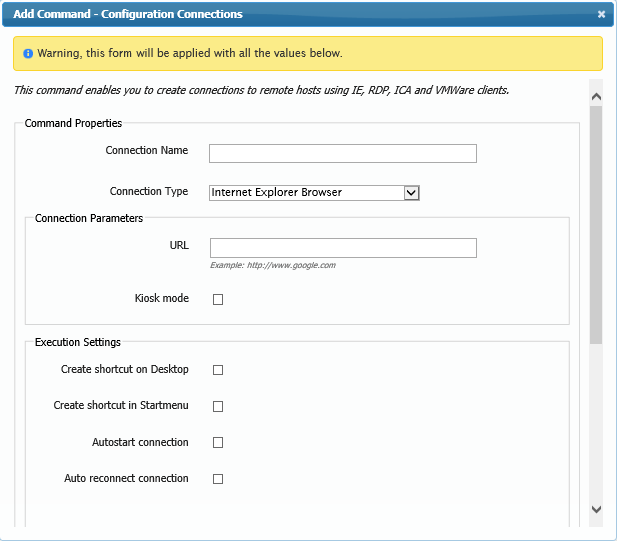
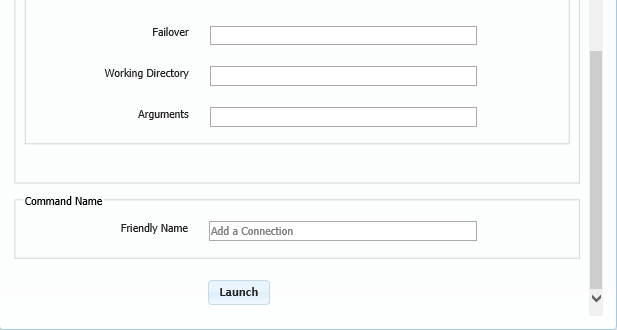
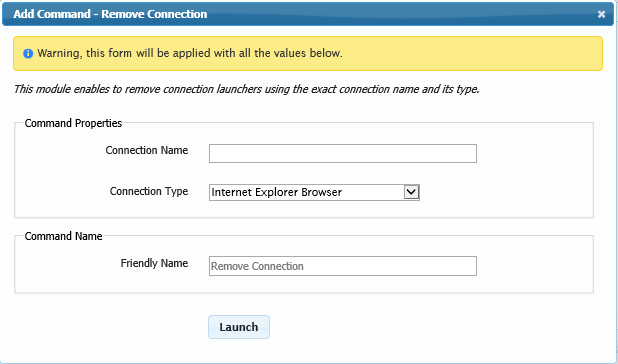
When using thin client devices, the administrator is able to create connections to remote hosts using IE, RDP, ICA and VMWare clients. These connections can then be deployed to other devices using the Clone Configuration function.
Add Connection
To add a new connection, click Add Connection command and fill in the appropriate fields in the Connection Parameters section.
Remove Connection
To remove a existing connection, click Remove Connection command and fill in the appropriate fields.
Device Configuration
The Device Configuration area contains commands for general configuration of target devices.
Keyboard Configuration
Using this command the administrator can change the language of a keyboard, its character repeat delay and repeat rate.
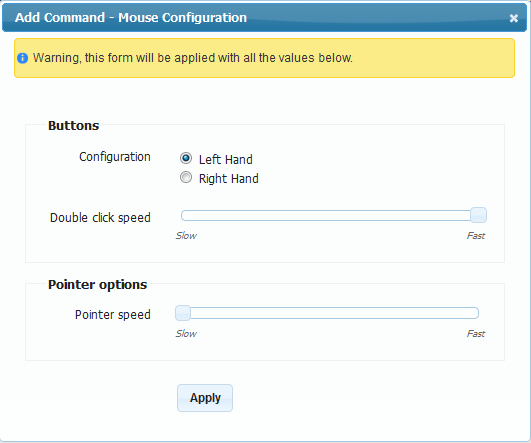
Mouse Configuration
Although rare, it may occasionally be necessary to configure a user’s mouse. Use the Mouse Configuration command to do so.
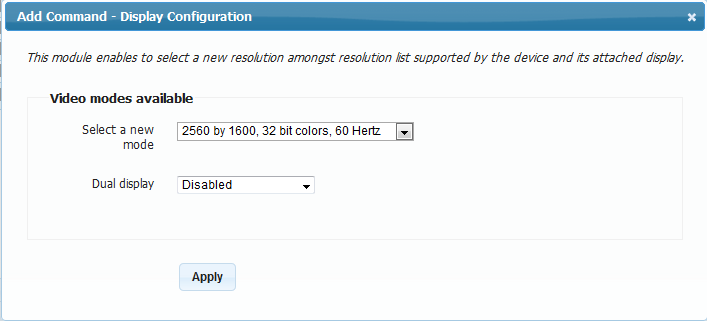
Display
Although all XcaliburW-approved target devices are configured to use DDC, there are occasions when the administrator may need to set a resolution manually. There will also be the need to set displays up to use dual screen modes and orientations. Use the Display command to configure these options.
 This command is executed using the Xcalibur W tray in order to be applied to the current user session. Please refer to Xcalibur W Tray section for more information This command is executed using the Xcalibur W tray in order to be applied to the current user session. Please refer to Xcalibur W Tray section for more information |
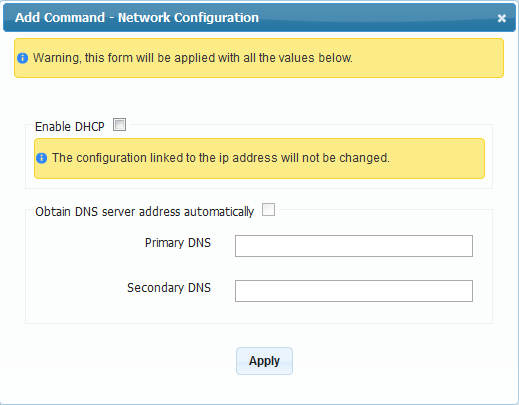
Network
Proxy
Some organizations require the configuration of target devices to use the company proxy server. The Proxy command allows these settings to be made by the Administrator using Xcalibur W.
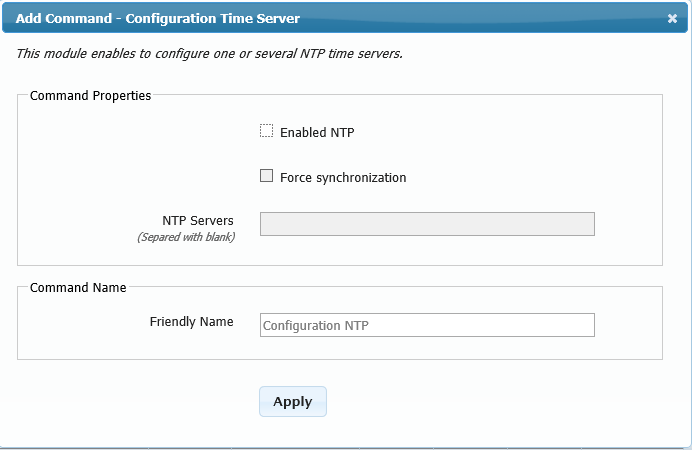
NTP
Time Zone
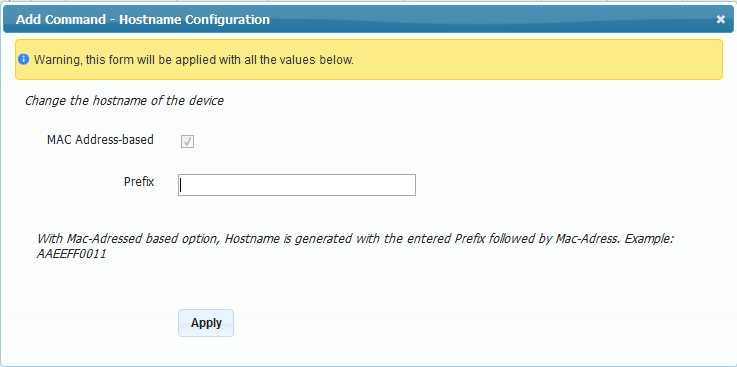
Hostname
In the event that the administrator needs to change host names they can do this using the Hostname command. This command also allows you to include the MAC ID as part of the hostname.
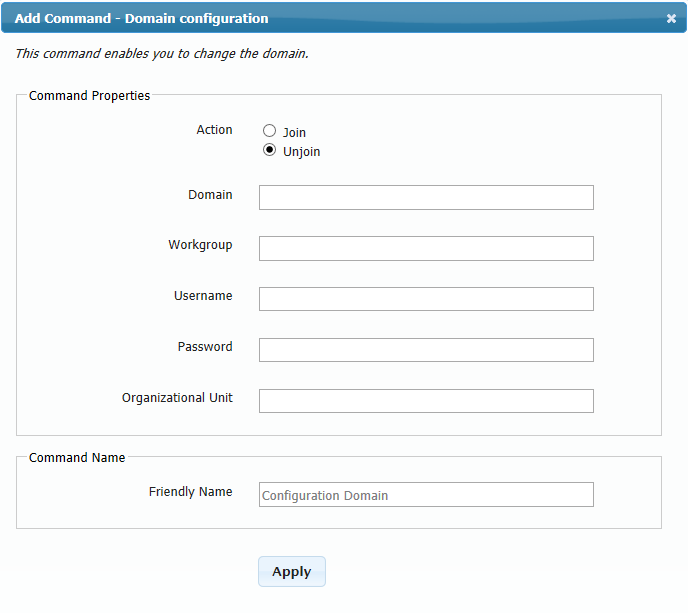
Domain
Users in large organizations sometimes need to manually join (or un-join) a domain. Use the Domain command to do this.
This command requires administrative access to the primary domain controller (PDC) (such as through a user account member of the Local Administrators or Domain Administrators groups). Therefore, the credentials must be entered into the Username and Password fields.
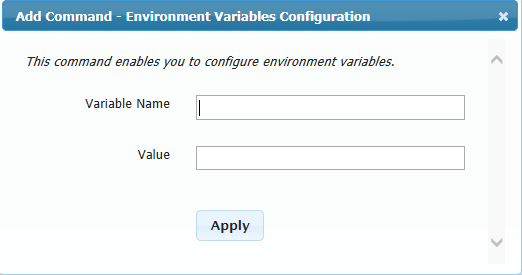
Environment Variables
Environment variables are strings that contain information such as drives, paths, or file names. They control the behavior of various programs. For example, the TEMP environment variable specifies the location in which programs should place temporary files.
The Environment Variables command allows the administrator to set new environment variables for the System account (not the current user account).
User Experience
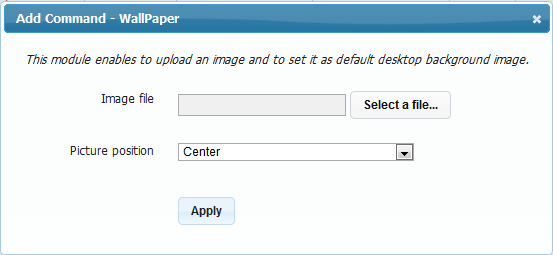
Wallpaper
The Wallpaper command allows you to modify the wallpaper of target devices using an image of your choice.
Image Management
This set of commands concentrates on the different OS image changes that may be required from time to time, such as application updates etc.
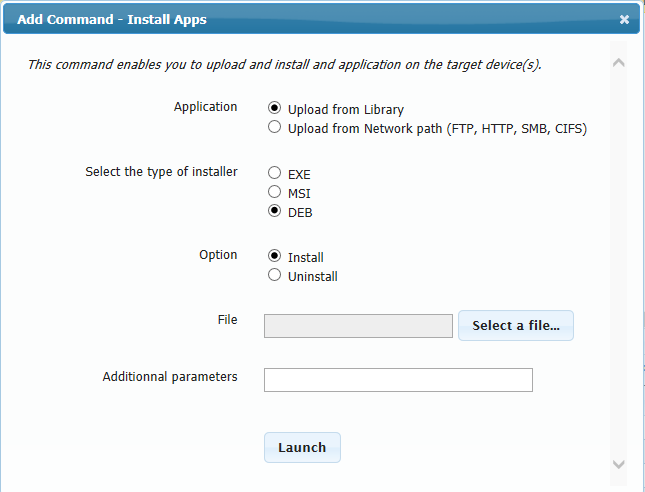
Install Apps
The Install Apps command allows administrators to deploy applications from a variety of sources to the target devices. Applications can be in either EXE and MSI formats for Windows platforms and DEB format for Linux platforms, and can be delivered via the Xcalibur W Library or FTP, HTTP, SMB or CIFS locations. In addition, execution parameters can also be specified.
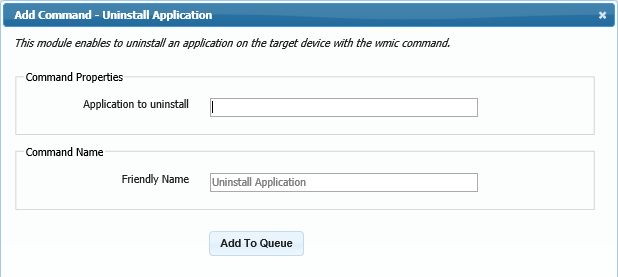
Uninstall Apps
The Uninstall Apps command allows administrators to Uninstall application using WMIC commands. Administrator shall specify the exact application name to proceed uinstallation.
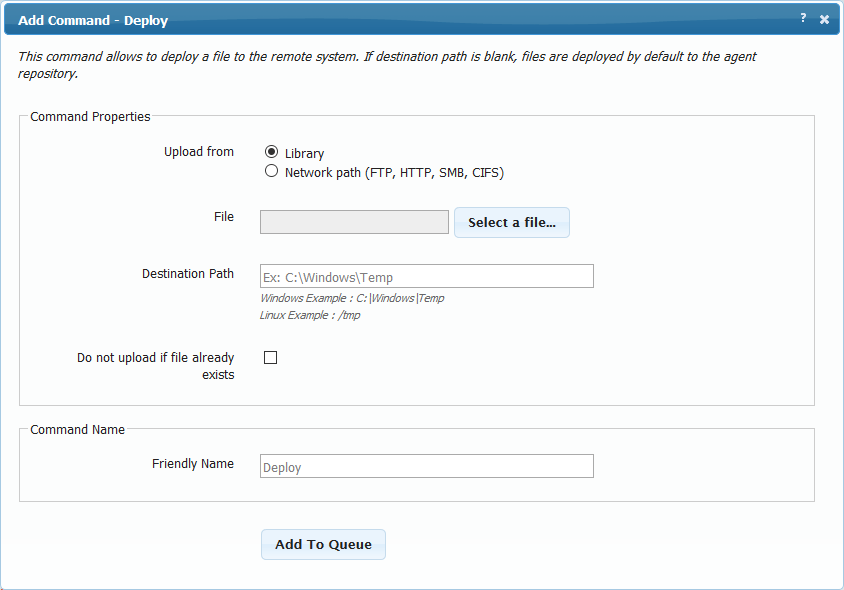
Deploy
The Deploy command is intended for use when you wish to upload a file or files to the target device(s).
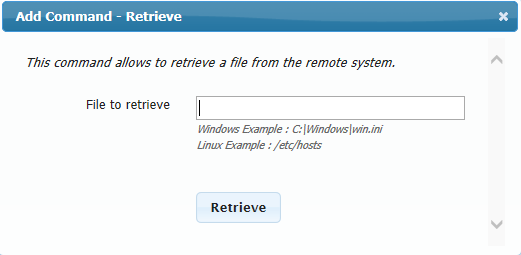
Retrieve
To recover a file from a target device (or devices), use the Retrieve command. Files downloaded are stored in the Library under Downloads.
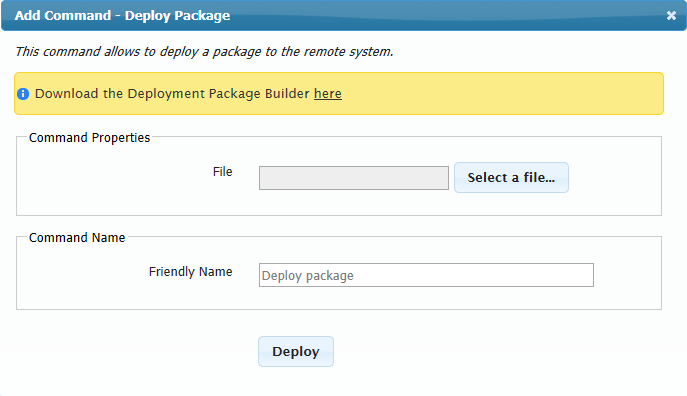
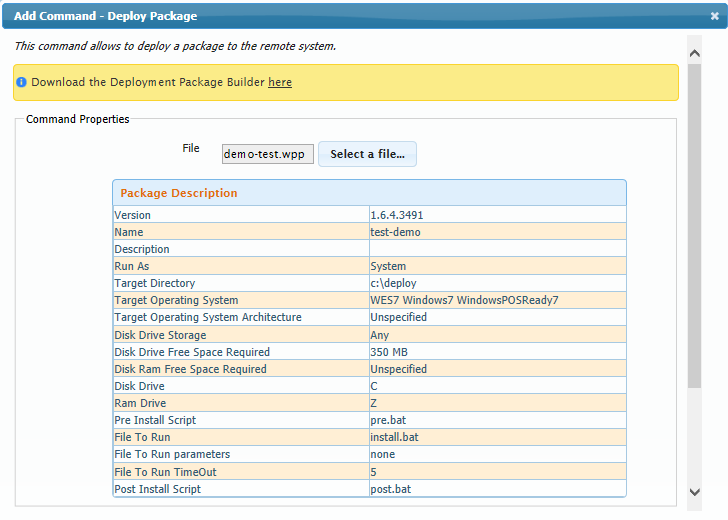
Deploy Package
The Deploy Package command enables distribution of software packages built with Xcalibur W's Package Builder. Click Select a File and then choose one of the available packages listed in your Library.
After selecting a package, Xcalibur W analyses the archive and displays the specifications of the package as shown in the image below. These data are Xcalibur W for information purpose only.
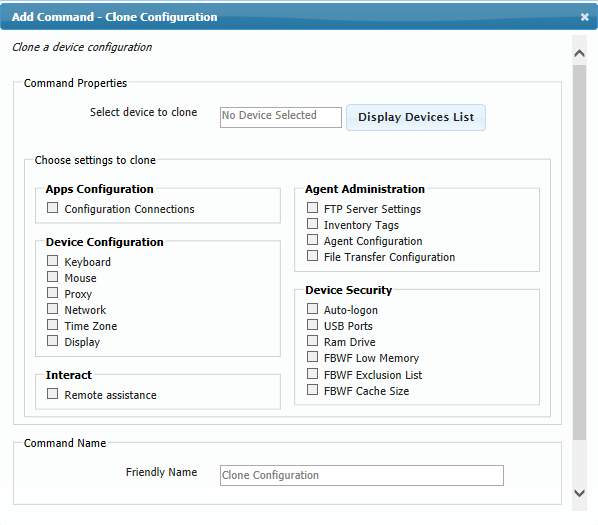
Clone Configuration
When managing hundreds or thousands of devices, it can be a challenge to distribute the same settings to multiple devices. Use the Clone Configuration command to clone the settings of one device to other devices.
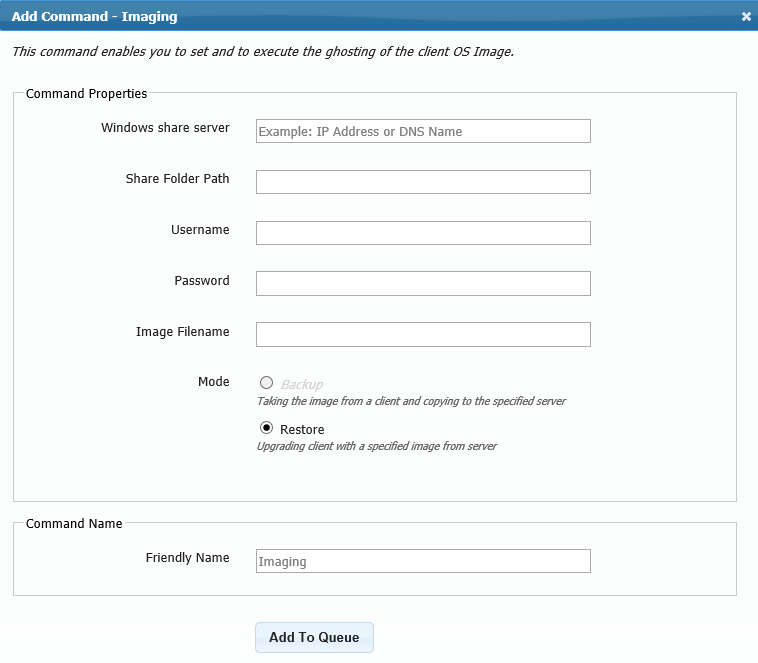
Imaging
Use the Imaging command to restore client images.This features is available for only for Windows 7 and Windows 8 platforms (including Embedded versions). Note also that the BCD bootloader shall be included in the system partition.
Please refer to Imaging Windows OS for further information on the Imaging process.